Welcome to the new FlexRadio Community! Please review the new Community Rules and other important new Community information on the Message Board.
Need the latest SmartSDR, Power Genius, Tuner Genius and Antenna Genius Software?
SmartSDR v3.7.4 and the SmartSDR v3.7.4 Release Notes | SmartSDR v2.12.1 and the SmartSDR v2.12.1 Release Notes
SmartSDR v1.12.1 and the SmartSDR v1.12.1 Release Notes
Power Genius XL Utility v3.8.8 and the Power Genius XL Release Notes v3.8.8
Tuner Genius XL Utility v1.2.11 and the Tuner Genius XL Release Notes v1.2.11
Antenna Genius Utility v4.1.8
SmartSDR v3.7.4 and the SmartSDR v3.7.4 Release Notes | SmartSDR v2.12.1 and the SmartSDR v2.12.1 Release Notes
SmartSDR v1.12.1 and the SmartSDR v1.12.1 Release Notes
Power Genius XL Utility v3.8.8 and the Power Genius XL Release Notes v3.8.8
Tuner Genius XL Utility v1.2.11 and the Tuner Genius XL Release Notes v1.2.11
Antenna Genius Utility v4.1.8
If you are having a problem, please refer to the product documentation or check the Help Center for known solutions.
Need technical support from FlexRadio? It's as simple as Creating a HelpDesk ticket.
Need technical support from FlexRadio? It's as simple as Creating a HelpDesk ticket.
Witch Norton or McAfee for 6600 M
Options
Brad
Member ✭✭
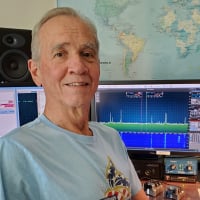
Have new computer(Win 10) that came with McAfee, but using Norton on my other computer. The new one will be for Ham Radio and the 6600M (if it ever gets here)only.
0
Answers
-
Brad, I am only using the built in Windows Defender.
Jeff
0 -
0
-
Neither. Both cause a lot of problems we get in support. I am just using Windows Defender and do not do careless things over the Internet.3
-
Hi Brad,
I've used a number of AV tools including Norton, Mcaffee and Symantec over the years. They all seem to cause problems at one time or another.
With Win10 I've been using Windows Defender and Malwarebytes and had good luck and no issues. Malwarebytes gets along with Windows defender and does catch things that Defender misses. The "real-time" protection is one example. Some web pages look safe but you can't always tell.
Curious to hear if others have also used and been happy with the Defender and Malwarebytes combination.

Al / NN4ZZ
al (at) nn4zz (dot) com
6700 & SSDR-W V 2.1.30
Win10
1 -
Consider the Bitdefender network appliance that protects your entire network.0
-
I have been using WEBROOT Secure Anywhere for several years without any issues on my Radio PC's running Win 10.
Tom W3FRG0 -
Thanks all. Am going to take Tim's advice and get rid of McAfee and use Windows defender. As am not using that computer except for the 6600 M and a few ham software.0
-
I second Tim's advice and use Windows Defender. and I also run Malware bytes exclusively on 6 machines running in my house.
Do be sure that you get rid of Macafee or Norton or any other AV package you have. Most companies do have removal tools available which work properly, download and use them. If you are really concerned, disconnect the Internet during the removal.
Also download the Windows Defender package before you start.
When you have finished removing Norton or whatever, REBOOT the computer TWICE, just in case there are stubs which are only removed at start time. Rebooting a second time is just belt and braces but for the extra time involved, worth doing.
Whatever you do, DO NOT run two AV programs at the same time. If you do, it can cause all sorts of weird behavior and slow running.
Tim0 -
Windows Defender and Malwarebytes0
-
Thanks for sharing the valuable information I also used Microsoft defender antivirus it is the best software for personal computer, but I have faced problem every week MS defender always ask for Gmail even I have already register Gmail id, regarding this I also consult to AOL customer support it provides the mail support service.
0 -
Tim, any problems running Kaspersky Total Security?0
-
Kaspersky is alleged to be spyware0
-
Technically Howard’s statement is accurate, but utterly incomplete. It was in fact proven by Israeli, US, and UK law enforcement and intelligence agencies that Kaspersky’s backend infrastructure was breached and the product was used to search for endpoints that contained specific information. Then the identified endpoints were targeted with real data exfiltration tools and methods. Kaspersky itself did not collect the data on behalf of the bad guys. The product itself works very well. SmartSDR has no problem with both Kaspersky and BitDefender. I also use the BitDefender network appliance/firewall to protect my entire network, which includes computers, SDRs, security cameras, ecobee smart thermostats, smart TVs, etc. Most of the malware gets blocked before it enters the network. Last but not least I use OpenDNS as an additional screening tool. Neither I (or the rest of the family) run Windows with admin rights and no ham software has ever ran or will run as admin.0
-
A side bar: Most of the systems that have been breached are not the actual target, but only the means of completing the mission or just being a stepping stone. Stuxnet was never about hacking Siemens, it was about Iran’s nuclear centrifuges. Hacking the PlayStation network was a failed attempt to build a distributed supercomputer for cracking encryption. The list goes on. Your personal data has been obtained long time ago, at scale, and enhanced by correlating multiple data points. My clients are paying me well to be paranoid. Let me give you a very crude example to illustrate the CONCEPT of conducting a complete threat analysis: A remotely accessible SDR with high gain directional antennas is a great asset to have in La Jolla, where we have strategic bases used by the Navy, the Marines, and the Secret Service, to name just a few. The SDR can be used for the following: 1) Remote listening post. It’s hard to build a stealthy surveillance site. Using a ham station that has been there for a long time is much more trivial. Hide it in plain sight 2) Use the radio is a command and control node for other on prem devices 3) High power jamming device should such a need araises Again, these are nothing but crude examples to illustrate that your computer or Flex may be used to accomplish missions objectIves that go beyond your personal secrets. You could merely be collateral damage.0
Leave a Comment
Categories
- All Categories
- 245 Community Topics
- 2.1K New Ideas
- 490 The Flea Market
- 7.4K Software
- 5.9K SmartSDR for Windows
- 135 SmartSDR for Maestro and M models
- 327 SmartSDR for Mac
- 243 SmartSDR for iOS
- 224 SmartSDR CAT
- 163 DAX
- 347 SmartSDR API
- 8.5K Radios and Accessories
- 6.9K FLEX-6000 Signature Series
- 767 Maestro
- 42 FlexControl
- 836 FLEX Series (Legacy) Radios
- 727 Genius Products
- 392 Power Genius XL Amplifier
- 251 Tuner Genius XL
- 84 Antenna Genius
- 222 Shack Infrastructure
- 149 Networking
- 370 Remote Operation (SmartLink)
- 118 Contesting
- 582 Peripherals & Station Integration
- 116 Amateur Radio Interests
- 810 Third-Party Software